reader comments
26 with 16 posters participating
Security researchers have uncovered a batch of Google Play apps that stole users’ text messages and made unauthorized purchases on users’ dime.
The malware, which was hidden in eight apps that had more than 700,000 downloads, hijacked SMS message notifications and then made unauthorized purchases, McAfee mobile researchers Sang Ryol Ryu and Chanung Pak said Monday. McAfee is calling the malware Android/Etinu.
User data free for the taking
The researchers said an investigation of the attacker-operated server that controlled infected devices showed it stored all kinds of date from users’ phones, including their mobile carrier, phone number, SMS messages, IP address, country, and network status. The server also stored auto-renewing subscriptions, some of which looked like this:
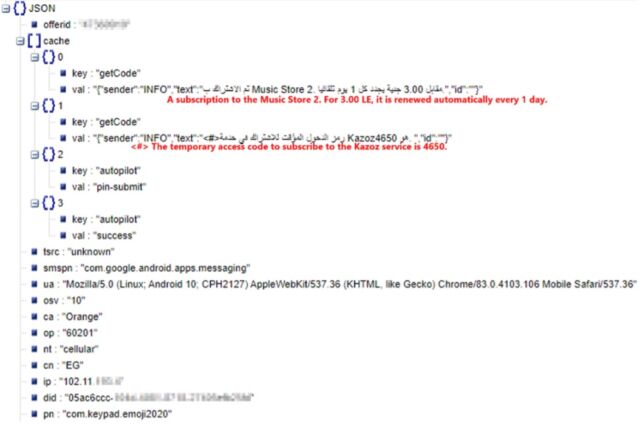
No joke
The malware is reminiscent, if not identical, to a prolific family of Android malware known as Joker, which also steals SMS messages and signs up users for pricey services.
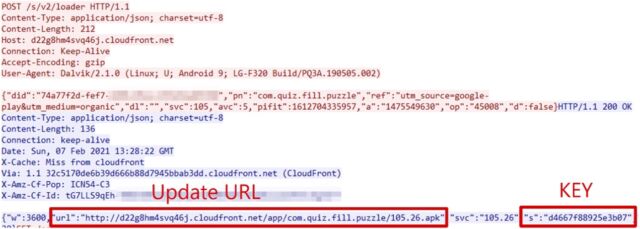
“The malware hijacks the Notification Listener to steal incoming SMS messages like Android Joker malware does, without the SMS read permission,” the researchers wrote referring to Etinu. “Like a chain system, the malware then passes the notification object to the final stage. When the notification has arisen from the default SMS package, the message is finally sent out using WebView JavaScript Interface.”
While the researchers say that Etinu is a malware family distinct from Joker, security software from Microsoft, Sophos, and other companies use the word Joker in their detection names of some of the newly discovered malicious apps. Etinu’s decryption flow and use of multi-stage payloads are also similar.
The apps and corresponding cryptographic hashes are:
| 08C4F705D5A7C9DC7C05EDEE3FCAD12F345A6EE6832D54B758E57394292BA651 | com.studio.keypaper2021 |
| CC2DEFEF5A14F9B4B9F27CC9F5BBB0D2FC8A729A2F4EBA20010E81A362D5560C | com.pip.editor.camera |
| 007587C4A84D18592BF4EF7AD828D5AAA7D50CADBBF8B0892590DB48CCA7487E | org.my.favorites.up.keypaper |
| 08FA33BC138FE4835C15E45D1C1D5A81094E156EEF28D02EA8910D5F8E44D4B8 | com.super.color.hairdryer |
| 9E688A36F02DD1B1A9AE4A5C94C1335B14D1B0B1C8901EC8C986B4390E95E760 | com.ce1ab3.app.photo.editor |
| 018B705E8577F065AC6F0EDE5A8A1622820B6AEAC77D0284852CEAECF8D8460C | com.hit.camera.pip |
| 0E2ACCFA47B782B062CC324704C1F999796F5045D9753423CF7238FE4CABBFA8 | com.daynight.keyboard.wallpaper |
| 50D498755486D3739BE5D2292A51C7C3D0ADA6D1A37C89B669A601A324794B06 | com.super.star.ringtones |
Some of the apps look like this:
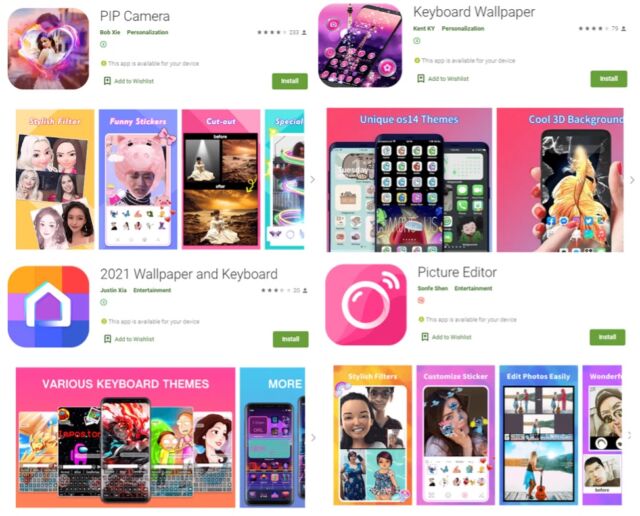
The researchers said they reported the apps to Google, and the company removed them.