reader comments
reader comments
48 with 40 posters participating
Log4Shell is the name given to a critical zeroday vulnerability that surfaced on Thursday when it was exploited in the wild in remote-code compromises against Minecraft servers. The source of the vulnerability was Log4J, a logging utility used by thousands if not millions of apps, including those used inside just about every enterprise on the planet. The Minecraft servers were the proverbial canary in the coal mine.
In the four days since, it’s clear Log4Shell is every bit as grave a threat as I claimed, with the list of cloud services affected reading like a who’s who of biggest names on the Internet. Threat analysts and researchers are still assessing the damage so far and the outlook over the next weeks and months. Here’s what you need to know for now.
What’s Log4J and what makes Log4Shell such a big deal? Log4J is an open-source Java-based logging tool available from Apache. It has the ability to perform network lookups using the Java Naming and Directory Interface to obtain services from the Lightweight Directory Access Protocol. The end result: Log4j will interpret a log message as a URL, go and fetch it, and even execute any executable payload it contains with the full privileges of the main program. Exploits are triggered inside text using the $ syntax, allowing them to be included in browser user agents or other commonly-logged attributes.
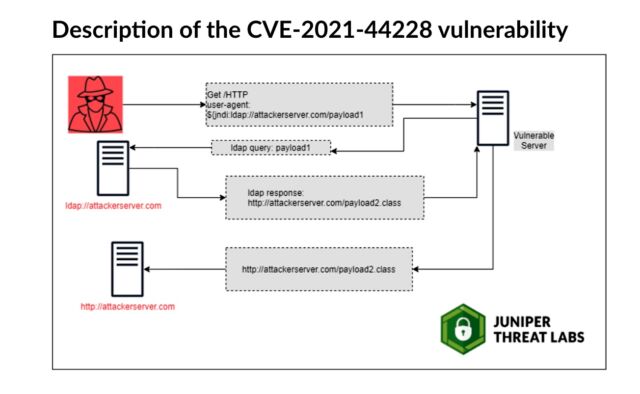
The vulnerability, tracked as CVE-2021-44228, has a severity rating of 10 out of 10. The zeroday has been exploited at least nine days before it surfaced.
Earliest evidence we’ve found so far of #Log4J exploit is 2021-12-01 04:36:50 UTC. That suggests it was in the wild at least 9 days before publicly disclosed. However, don’t see evidence of mass exploitation until after public disclosure.
— Matthew Prince ? (@eastdakota) December 11, 2021
Researchers at Cisco’s Talos security team said they observed exploits beginning December 2.
What has happened since Log4Shell surfaced last Thursday? Almost immediately, security firm Greynoise detected active scanning attempting to identify vulnerable servers. Researchers report seeing this critical and easy-to-exploit vulnerability being used to install crypto-mining malware, bolster Linux botnets, and exfiltrate configurations, environmental variables, and other potentially sensitive data from vulnerable servers.
What’s the prognosis? In a best-case scenario, major brokerages, banks, and merchants will invest huge sums in overtime costs to pay large numbers of already overworked IT employees to mop up this mess during the holidays. You don’t want to think about the worst-case scenario, other than to remember the 2017 breach of Equifax, and the resulting compromise of 143 million US consumers’ data that followed when that company failed to patch against a similarly devastating vulnerability.
Sounds bad. What should I do? Yeah, it is. If an end user, there’s not much you can do other than to hound the services you use and ask what they’re doing to keep the data you entrust with them secure. The most useful thing the cloud services can do is to update Log4J. But for large enterprises, it’s often not that simple. Dozens of security companies have published guidance. Advice from Microsoft and Sophos is here and here.