reader comments
47 with
Researchers have devised a low-cost smartphone attack that cracks the authentication fingerprint used to unlock the screen and perform other sensitive actions on a range of Android devices in as little as 45 minutes.
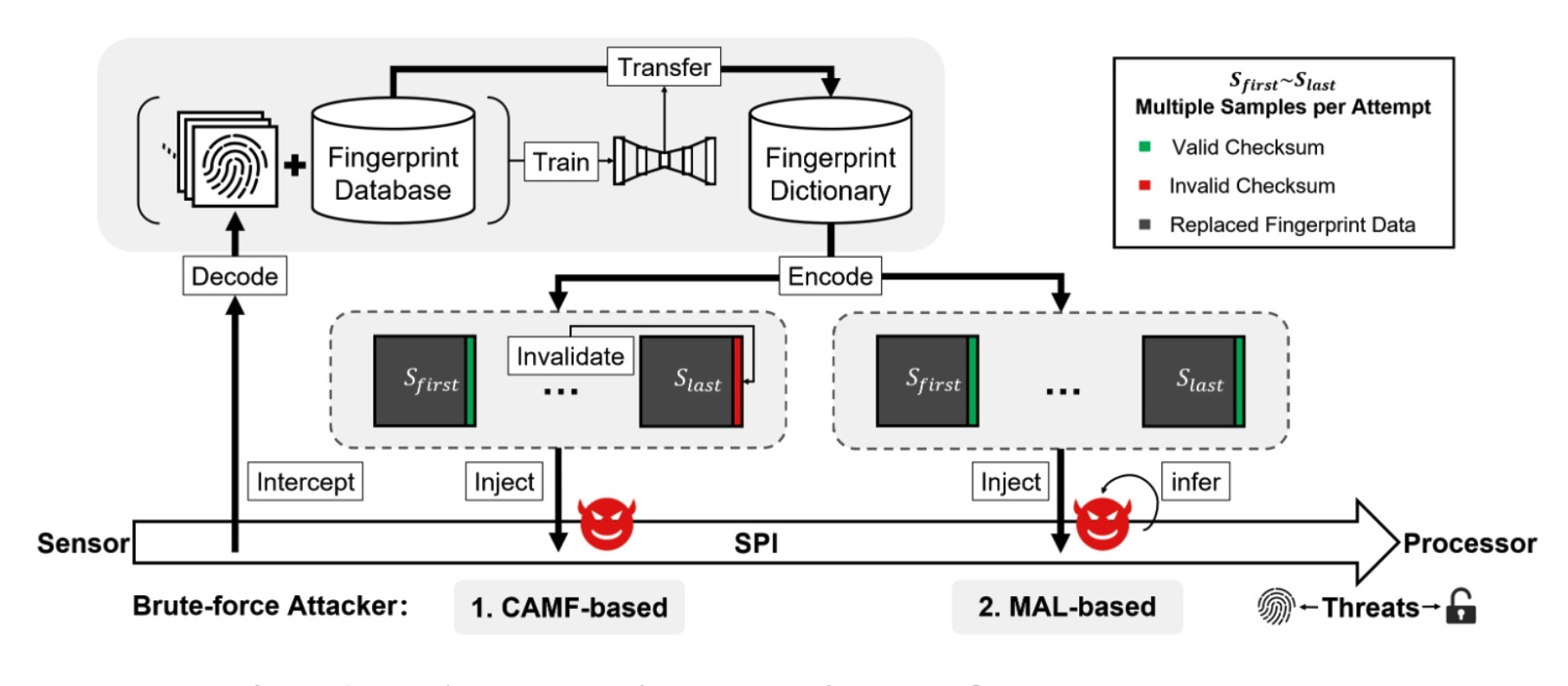
Dubbed BrutePrint by its creators, the attack requires an adversary to have physical control of a device when it is lost, stolen, temporarily surrendered, or unattended, for instance, while the owner is asleep. The objective: to gain the ability to perform a brute-force attack that tries huge numbers of fingerprint guesses until one is found that will unlock the device. The attack exploits vulnerabilities and weaknesses in the device SFA (smartphone fingerprint authentication).
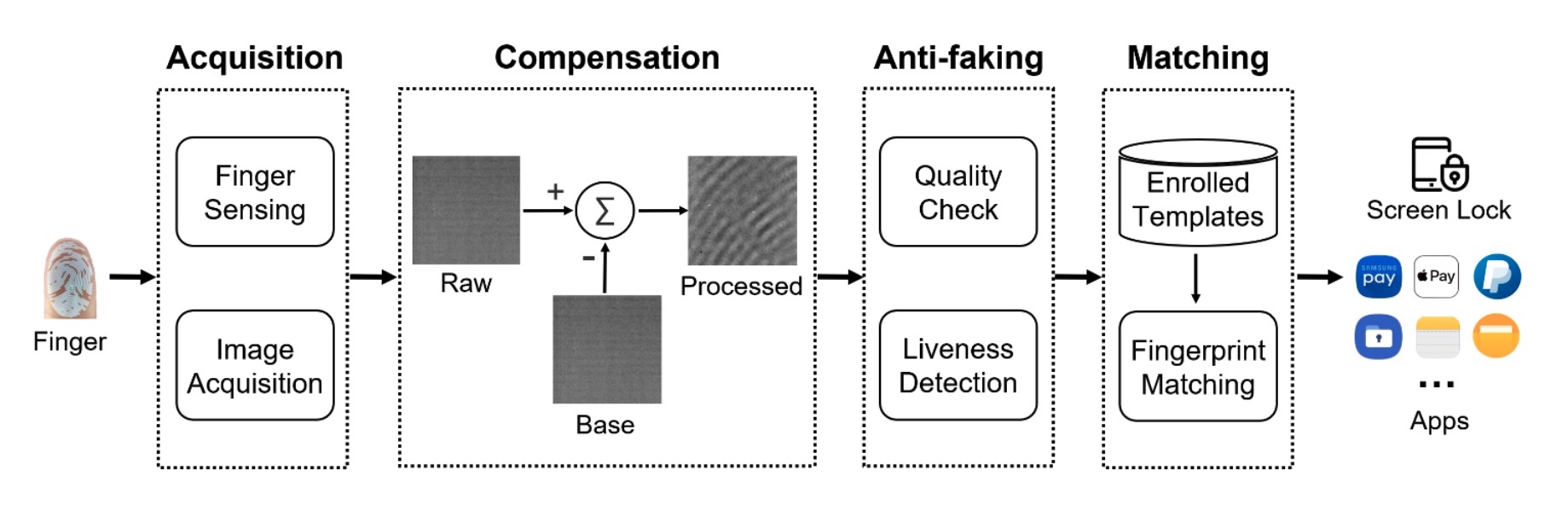
BrutePrint overview
BrutePrint is an inexpensive attack that exploits vulnerabilities that allow people to unlock devices by exploiting various vulnerabilities and weaknesses in smartphone fingerprint authentication systems. Here’s the workflow of these systems, which are typically abbreviated as SFAs.
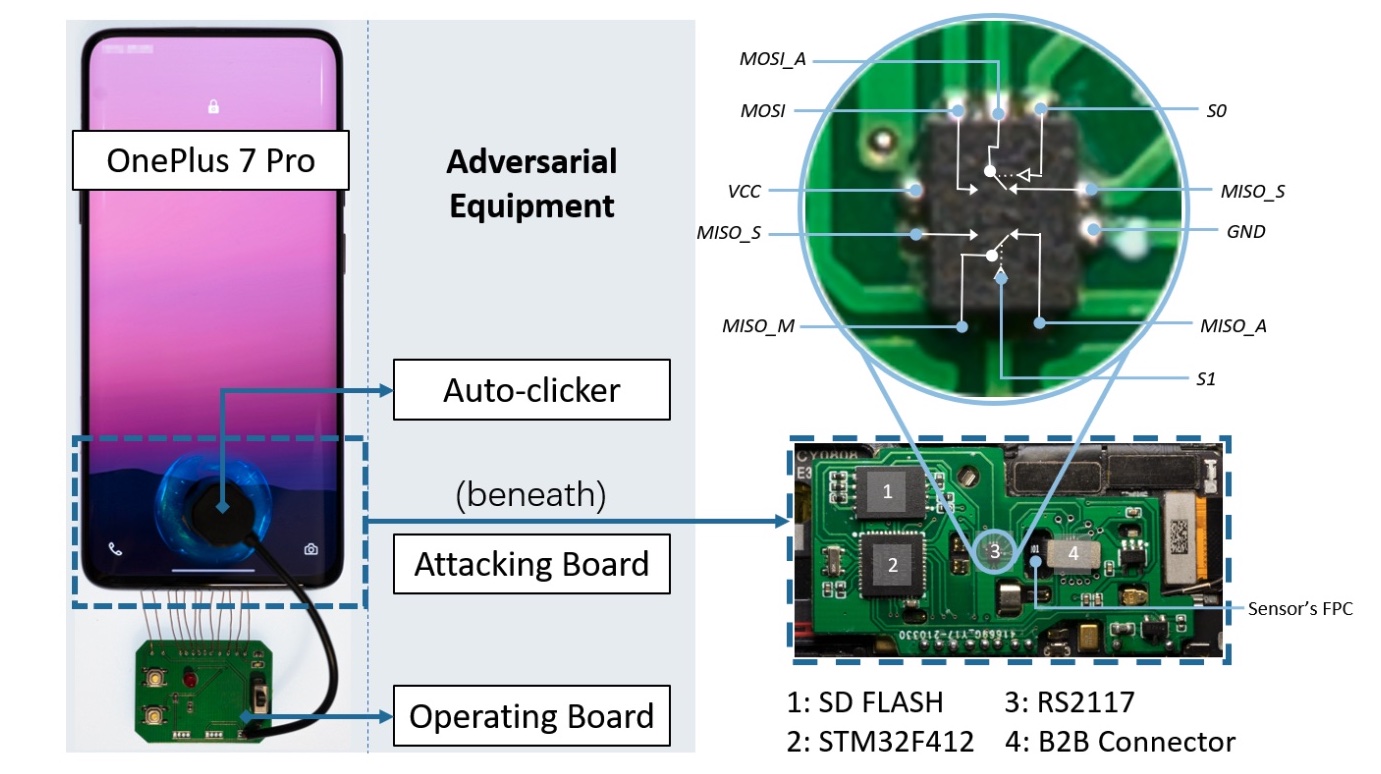
The core of the equipment required for BrutePrint is a $15 circuit board that contains (1) an STM32F412 microcontroller from STMicroelectronics, (2) a bidirectional, dual-channel, analog switch known as an RS2117, (3) an SD flash card with 8GB of memory, and (4) a board-to-board connector that connects to the phone motherboard to the fingerprint flexible printed circuit of the fingerprint sensor.
Additionally, the attack requires a database of fingerprints, similar to those used in research or leaked in real-world breaches such as these.
Not all smartphones are created equal
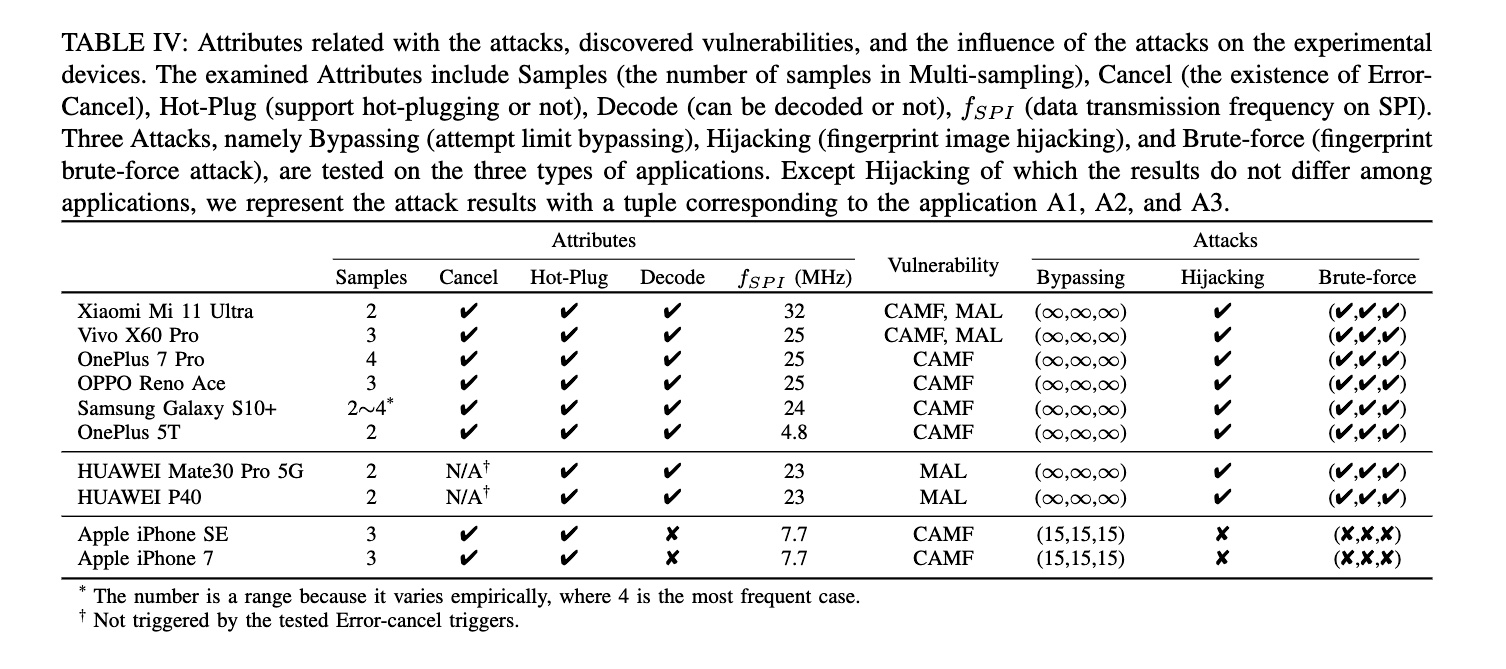
More on how BrutePrint works later. First, a breakdown of how various phone models fared. In all, the researchers tested 10 models: Xiaomi Mi 11 Ultra, Vivo X60 Pro, OnePlus 7 Pro, OPPO Reno Ace, Samsung Galaxy S10+, OnePlus 5T, Huawei Mate30 Pro 5G, Huawei P40, Apple iPhone SE, Apple iPhone 7.
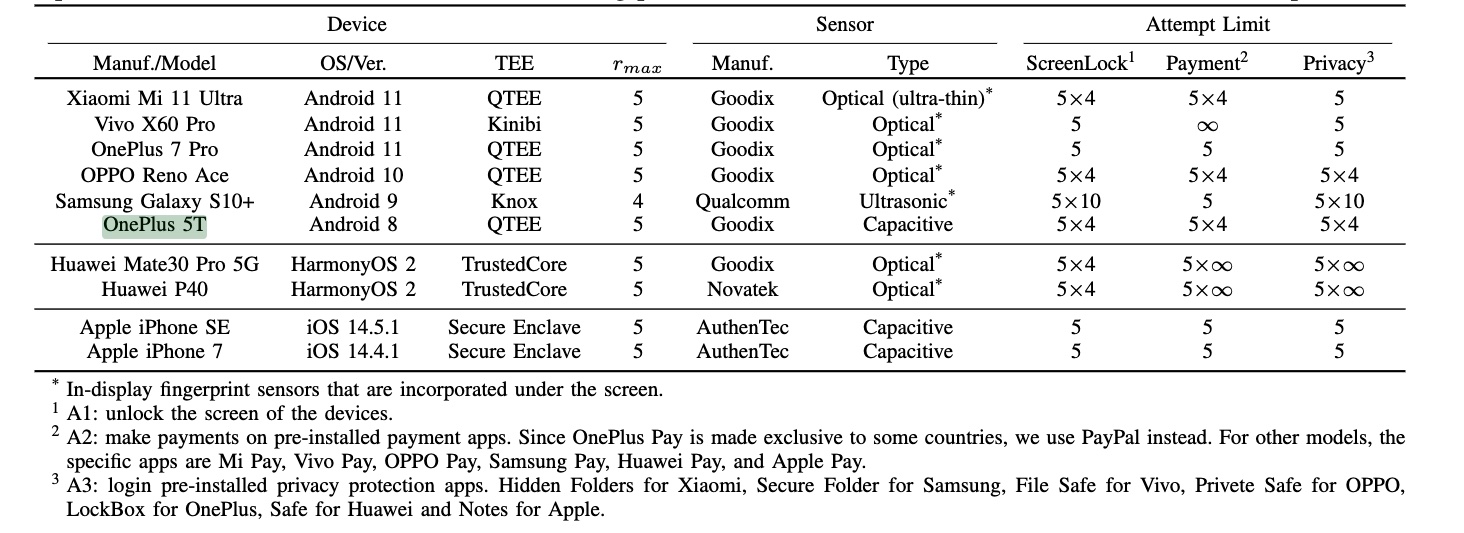
The researchers tested each for various vulnerabilities, weaknesses, or susceptibility to various attack techniques. Examined attributes included the number of samples in multi-sampling, the existence of error-cancel, support for hot-plugging, whether data could be decoded, and data transmission frequency on SPI. Additionally, the researchers tested three attacks: attempted limit bypassing, hijacking of fingerprint images, and fingerprint brute-forcing.
Last, the researchers provided results showing the time it took for various phones to have their fingerprints brute-forced. Because the amount of time depends on the number of prints authorized, the researchers set each to a single print.
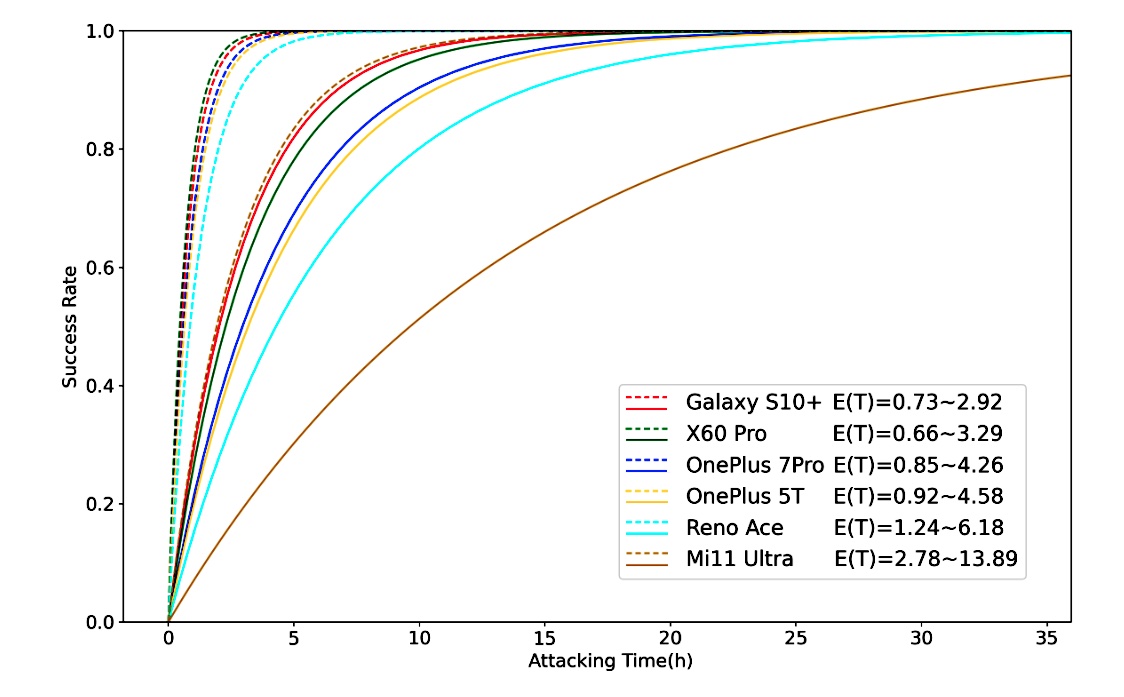
Although specifics varied, the result is that BrutePrint can attempt an unlimited number of authentication fingerprints on all eight of the Android models tested. Depending on various factors, including the fingerprint authentication framework of a specific phone and the number of fingerprints stored for authentication, it takes anywhere from about 40 minutes to 14 hours.