Enlarge (credit: Getty Images)

The output of PHP servers infected by TellYouThePass ransomware. (credit: Censys)
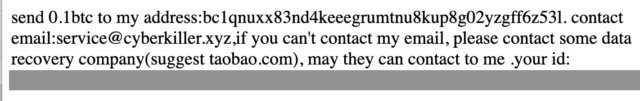
The accompanying ransom note. (credit: Censys)
When opportunity knocks
The vulnerability, tracked as CVE-2024-4577 and carrying a severity rating of 9.8 out of 10, stems from errors in the way PHP converts Unicode characters into ASCII. A feature built into Windows known as Best Fit allows attackers to use a technique known as argument injection to convert user-supplied input into characters that pass malicious commands to the main PHP application. Exploits allow attackers to bypass CVE-2012-1823, a critical code execution vulnerability patched in PHP in 2012.
Read 11 remaining paragraphs | Comments
Article Tags:
featuredArticle Categories:
Technology