reader comments
24 with 19 posters participating
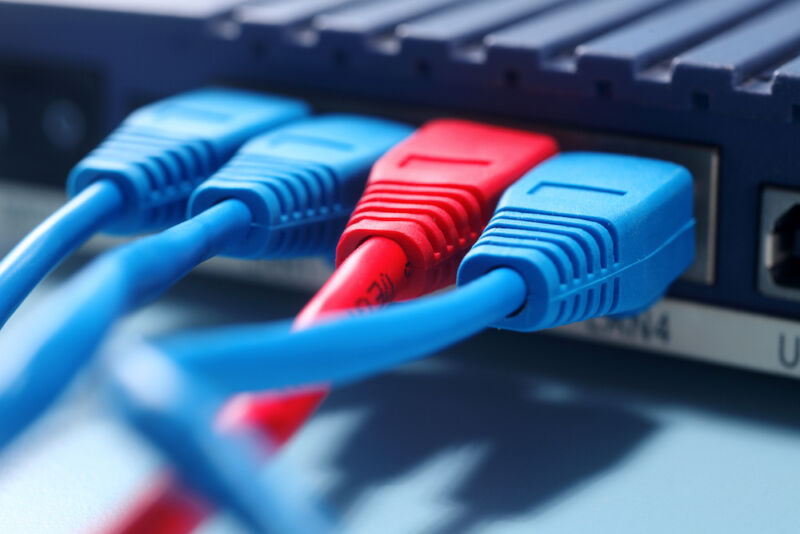
For years, malicious hackers have been hacking large fleets of MikroTik routers and conscripting them into Trickbot, one of the Internet’s most destructive botnets. Now, Microsoft has finally figured out why and how the devices are being put to use.
Trickbot came to light in 2016 as a trojan for stealing account passwords for use in bank fraud. Since then, it has mushroomed into one of the Internet’s most aggressive threat platforms, thanks to its highly modular, multi-stage malware framework that provides a full suite of tools that are used to install ransomware and other forms of malware from other hacking groups.
The malware driving Trickbot is notable for its advanced capabilities. It excels at gaining powerful administrator privileges, spreading rapidly from computer to computer in networks, and performing reconnaissance that identifies infected computers belonging to high-value targets. It often uses readily available software like Mimikatz or exploits like EternalBlue stolen from the National Security Agency.
Hiding the C2
Trickbot operators, Microsoft said on Wednesday, are compromising MikroTik devices and using them to conceal the location of the command-and-control servers that exchange data and commands with infected computers. Instead of infected computers connecting directly to the control servers, they connect to the compromised routers, which act as go-betweens.
When security analysts monitor the connections infected computers make, the researchers see IP addresses belonging to compromised routers inside homes and businesses. The location of the control servers themselves remains hidden and can’t be detected without access to the proxy router. Here’s an overview:
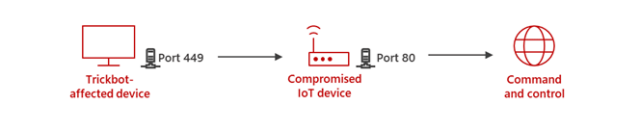
“The purpose of Trickbot using MikroTik devices is to create a line of communication between the Trickbot-affected device and the C2 server that standard defense systems in the network are not able to detect,” Microsoft researchers wrote. “The attackers begin by hacking into a MikroTik router.”
300,000 MikroTik routers.
Once the operators take control of a device, they change the password to prevent anyone else from remotely regaining control.






