
reader comments
42 with 34 posters participating, including story author
For more than a decade, we’ve been promised that a world without passwords is just around the corner, and yet year after year, this security nirvana proves out of reach. Now, for the first time, a workable form of passwordless authentication is about to become available to the masses in the form of a standard adopted by Apple, Google, and Microsoft that allows for cross-platform and cross-service passkeys.
Password-killing schemes pushed in the past suffered from a host of problems. A key shortcoming was the lack of a viable recovery mechanism when someone lost control of phone numbers or physical tokens and phones tied to an account. Another limitation was that most solutions ultimately failed to be, in fact, truly passwordless. Instead, they gave users options to log in with a face scan or fingerprint, but these systems ultimately fell back on a password, and that meant that phishing, password reuse, and forgotten passcodes—all the reasons we hated passwords to begin with—didn’t go away.
A new approach
What’s different this time is that Apple, Google, and Microsoft all seem to be on board with the same well-defined solution. Not only that, but the solution is easier than ever for users, and it’s less costly for big services like Github and Facebook to roll out. It has also been painstakingly devised and peer-reviewed by experts in authentication and security.
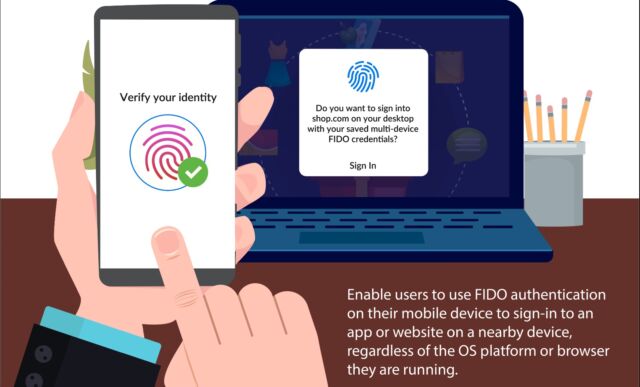
The current multifactor authentication (MFA) methods have made important strides over the past five years. Google, for instance, allows me to download an iOS or Android app that I use as a second factor when logging in to my Google account from a new device. Based on CTAP—short for client to authenticator protocol—this system uses Bluetooth to ensure that the phone is in proximity to the new device and that the new device is, in fact, connected to Google and not a site masquerading as Google. That means it’s unphishable. The standard ensures that the cryptographic secret stored on the phone can’t be extracted.
Advanced Protection Program that requires physical keys in the form of standalone dongles or end-user phones to authenticate logins from new devices.
The big limitation right now is that MFA and passwordless authentication get rolled out differently—if at all—by each service provider. Some providers, like most banks and financial services, still send one-time passwords through SMS or email. Recognizing that those aren’t secure means for transporting security-sensitive secrets, many services have moved on to a method known as TOTP—short for Time-based one-time password—to allow the addition of a second factor, which effectively augments the password with the “something I have” factor.
Physical security keys, TOTPs, and to a lesser extent two-factor authentication through SMS and email represent an important step forward, but there remain three key limitations. First, TOTPs generated through authenticator apps and sent by text or email are phishable, the same way regular passwords are. Second, each service has its own closed MFA platform. That means that even when using unphishable forms of MFA—such as standalone physical keys or phone-based keys—a user needs a separate key for Google, Microsoft, and every other Internet property. To make matters worse, each OS platform has differing mechanisms for implementing MFA.
These problems give way to a third one: the sheer unusability for most end users and the nontrivial cost and complexity each service faces when trying to offer MFA.






