reader comments
22 with 18 posters participating
From the what-could-possibly-go-wrong files comes this: An industrial control engineer recently made a workstation part of a botnet after inadvertently installing malware advertising itself as a means for recovering lost passwords.
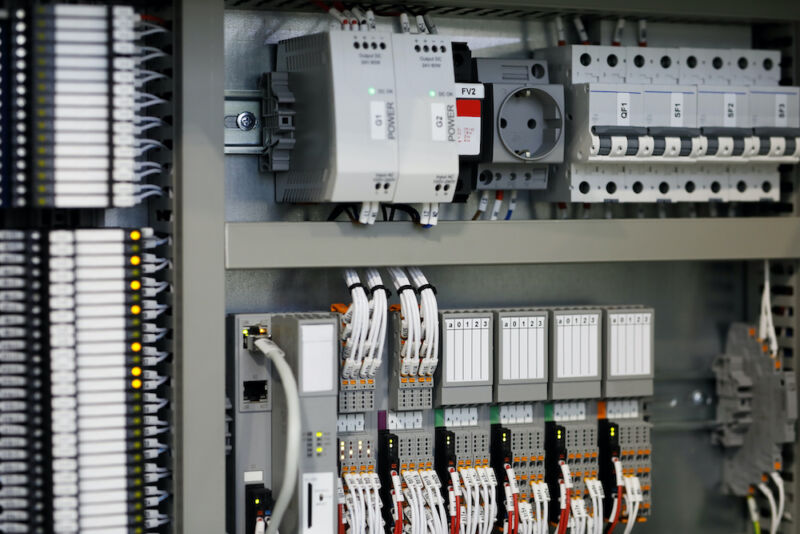
Lost passwords happen in many organizations. A programmable logic controller—used to automate processes inside factories, electric plants, and other industrial settings—may be set up and largely forgotten over the following years. When a replacement engineer later identifies a problem affecting the PLC, they can discover the now long-gone original engineer never left the passcode behind before departing the company.
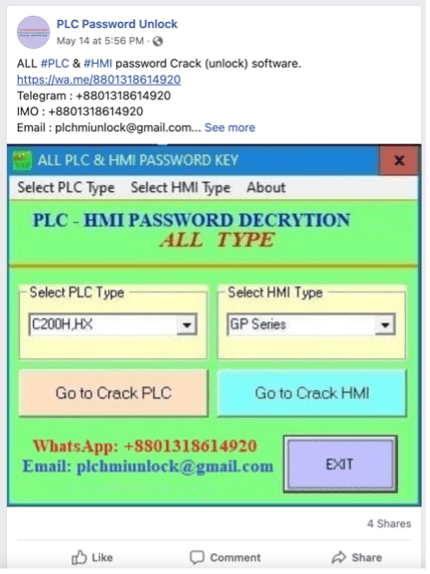
According to a blog post from security firm Dragos, an entire ecosystem of malware attempts to capitalize on scenarios like this one inside industrial facilities. Online advertisements like those below promote password crackers for PLCs and human-machine interfaces, which are the workhorses inside these environments.

When your industrial system is part of a botnet
Dragos—which helps firms secure industrial control systems against ransomware, state-sponsored hackers, and potential saboteurs—recently performed a routine vulnerability assessment and discovered a customer’s system had run software that was able to successfully recover the plaintext password for the DirectLogic 06, a PLC sold by Automation Direct. The software recovered the password, but not through the normal method of cracking the cryptographic hash. Instead, the software exploited a zero-day vulnerability in Automatic Direct PLCs that exposed the passcode.
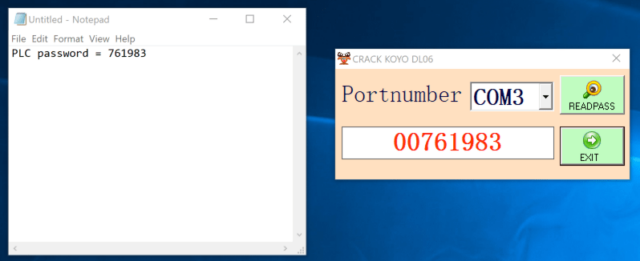
“Previous research targeting DirectLogic PLCs has resulted in successful cracking techniques,” Dragos researcher Sam Hanson wrote. “However, Dragos found that this exploit does not crack a scrambled version of the password as historically seen in popular exploitation frameworks. Instead, a specific byte sequence is sent by the malware dropper to a COM port.”
![]()
The vulnerability, and a related one also found by Hanson, have now been patched and are tracked as CVE-2022-2033 and CVE-2022-2004. The latter vulnerability can recover passwords and send them to a remote hacker, bringing the severity rating to 7.5 out of a possible 10.
Besides recovering the password, the software installed on the Dragos customer’s network also installed malware known as Sality. It made the infected system part of a botnet and monitored the clipboard of the infected workstation every half second for any data related to cryptocurrency wallet addresses.
“If seen, the hijacker replaces the address with one owned by the threat actor,” Hanson said. “This in-real-time hijacking is an effective way to steal cryptocurrency from users wanting to transfer funds and increases our confidence that the adversary is financially motivated.”
Hanson went on to say that he has found password crackers advertised online for a wide range of industrial software sold by other companies. They include:
| Vendor and Asset | System Type |
| Automation Direct DirectLogic 06 | PLC |
| Omron CP1H | PLC |
| Omron C200HX | PLC |
| Omron C200H | PLC |
| Omron CPM2* | PLC |
| Omron CPM1A | PLC |
| Omron CQM1H | PLC |
| Siemens S7-200 | PLC |
| Siemens S7-200 | Project File (*.mwp) |
| Siemens LOGO! 0AB6 | PLC |
| ABB Codesys | Project File (*.pro) |
| Delta Automation DVP, ES, EX, SS2, EC Series | PLC |
| Fuji Electric POD UG | HMI |
| Fuji Electric Hakko | HMI |
| Mitsubishi Electric FX Series (3U and 3G) | PLC |
| Mitsubishi Electric Q02 Series | PLC |
| Mitsubishi Electric GT 1020 Series | HMI |
| Mitsubishi Electric GOT F930 | HMI |
| Mitsubishi Electric GOT F940 | HMI |
| Mitsubishi Electric GOT 1055 | HMI |
| Pro-Face GP Pro-Face | HMI |
| Pro-Face GP | Project File (*.prw) |
| Vigor VB | PLC |
| Vigor VH | PLC |
| Weintek | HMI |
| Allen Bradley MicroLogix 1000 | PLC |
| Panasonic NAIS F P0 | PLC |
| Fatek FBe and FBs Series | PLC |
| IDEC Corporation HG2S-FF | HMI |
| LG K80S | PLC |
| LG K120S | PLC |
Dragos tested only the malware targeting the DirectLogic devices, but a rudimentary analysis of a few samples indicated they also contained malware.
“In general, it appears there is an ecosystem for this type of software,” Hanson said. “Several websites and multiple social media accounts exist all touting their password ‘crackers.’”
The account is concerning because it illustrates the laxness that continues to operate in many industrial control settings. The criminals behind the malware infecting the Dragos customer were after money, but there’s no reason more malicious hackers out to sabotage a dam, power plant, or similar facility couldn’t perform a similar intrusion with much more severe consequences.






