reader comments
135 with
Millions of US military emails have been misdirected to Mali through a “typo leak” that has exposed highly sensitive information, including diplomatic documents, tax returns, passwords, and the travel details of top officers.
Despite repeated warnings over a decade, a steady flow of email traffic continues to the .ML domain, the country identifier for Mali, as a result of people mistyping .MIL, the suffix to all US military email addresses.
The problem was first identified almost a decade ago by Johannes Zuurbier, a Dutch Internet entrepreneur who has a contract to manage Mali’s country domain.
Zuurbier has been collecting misdirected emails since January in an effort to persuade the US to take the issue seriously. He holds close to 117,000 misdirected messages—almost 1,000 arrived on Wednesday alone. In a letter he sent to the US in early July, Zuurbier wrote: “This risk is real and could be exploited by adversaries of the US.”
Control of the .ML domain will revert on Monday from Zuurbier to Mali’s government, which is closely allied with Russia. When Zuurbier’s 10-year management contract expires, Malian authorities will be able to gather the misdirected emails. The Malian government did not respond to requests for comment.
Zuurbier, managing director of Amsterdam-based Mali Dili, has approached US officials repeatedly, including through a defense attaché in Mali, a senior adviser to the US National Cyber Security Service, and even White House officials.
Much of the email flow is spam, and none is marked as classified. But some messages contain highly sensitive data on serving US military personnel, contractors, and their families.
Their contents include X-rays and medical data, identity document information, crew lists for ships, staff lists at bases, maps of installations, photos of bases, naval inspection reports, contracts, criminal complaints against personnel, internal investigations into bullying, official travel itineraries, bookings, and tax and financial records.
Mike Rogers, a retired American admiral who used to run the National Security Agency and the US Army’s Cyber Command, said: “If you have this kind of sustained access, you can generate intelligence even just from unclassified information.”
“This is not uncommon,” he added. “It’s not out of the norm that people make mistakes but the question is the scale, the duration, and the sensitivity of the information.”
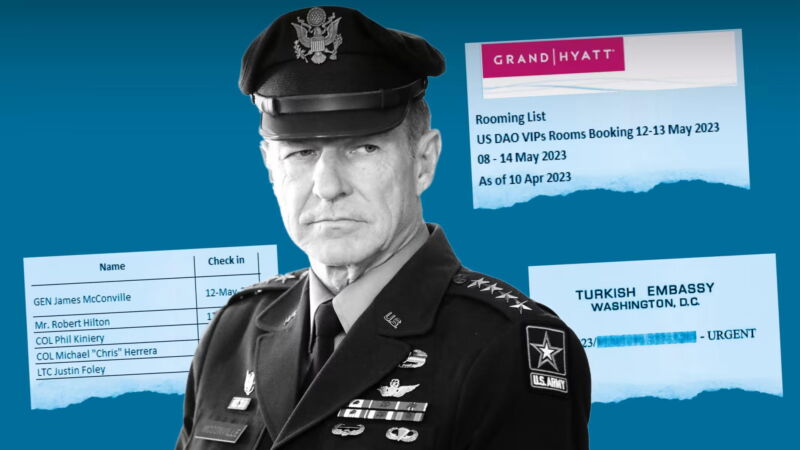
One misdirected email this year included the travel plans for General James McConville, the chief of staff of the US Army, and his delegation for a then-forthcoming visit to Indonesia in May.
The email included a full list of room numbers, the itinerary for McConville and 20 others, as well as details of the collection of McConville’s room key at the Grand Hyatt Jakarta, where he received a VIP upgrade to a grand suite.
Rogers warned the transfer of control to Mali posed a significant problem. “It’s one thing when you are dealing with a domain administrator who is trying, even unsuccessfully, to articulate the concern,” said Rogers. “It’s another when it’s a foreign government that… sees it as an advantage that they can use.”
Lt. Cmdr Tim Gorman, a spokesman for the Pentagon, said the Department of Defense “is aware of this issue and takes all unauthorized disclosures of controlled national security information or controlled unclassified information seriously.”
He said that emails sent directly from the .mil domain to Malian addresses “are blocked before they leave the .mil domain and the sender is notified that they must validate the email addresses of the intended recipients.”