
Enlarge / Supply-chain attacks, like the latest PyPI discovery, insert malicious code into seemingly functional software packages used by developers. They’re becoming increasingly common. (credit: Getty Images)
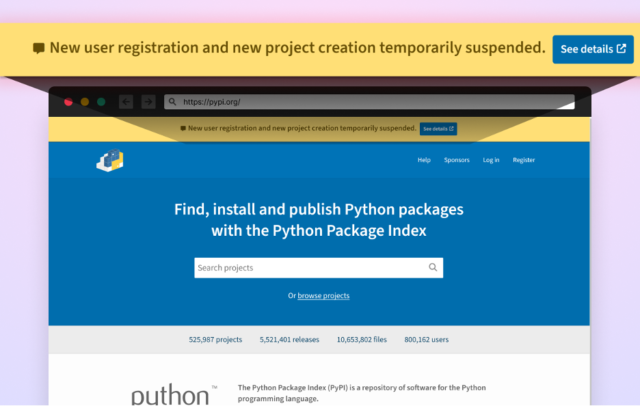
Screenshot showing temporary suspension notification. (credit: Checkmarx)
About 10 hours later, PyPI restored new project creation and new user registration. Once again, the site provided no reason for the 10-hour halt.
Read 10 remaining paragraphs | Comments
Article Tags:
featuredArticle Categories:
Technology





